Image: Naval Dome
Cyber- strikes on the maritime market’s functional innovation (OT) systems have actually enhanced by 900% over the last 3 years, with the variety of reported cases readied to get to document quantities by year end.
In an on the internet discussion forum recently, Robert Rizika, Head of North American Operations at maritime cybersecurity expert Naval Dome, informed port as well as incurable drivers that while 50 considerable OT hacks were reported in 2017, that number enhanced to 120 in 2018 as well as greater than 310 in 2014. This year is appearing like it will certainly finish with greater than 500 significant cyber safety and security violations, claimed Rizka, with considerably even more going unreported.
Speaking throughout the 2020 Port Security Seminar & & Expo, a week-long digital meeting arranged by the American Association of Port Authorities, Rizika claimed that given that NotPetya– the infection that led to a $300 million loss for Maersk– “attacks are increasing at an alarming rate”.
Recalling current strikes, he informed delegates that in 2018 the initial ports were influenced, with Barcelona, after that San Diego dropping under fire. Australian shipbuilder Austal was struck as well as the strike on COSCO removed fifty percent of the shipowner’s UNITED STATE network.
This year, a U.S,-based gas pipe driver as well as delivery firm MSC have actually been struck by malware– with the MSC event closing down the shipowner’s Geneva, Switzerland, HQ for 5 days. A U.S.-based freight center’s os were contaminated with the Ryuk ransomware as well as last month the OT systems at Iran’s Shahid Rajee port were hacked, limiting all framework activities, producing a large back log.
Reports of this strike have actually gone some method elevating public recognition of the prospective larger effect of cyber hazards on ports all over the world. Intelligence from Iran, together with electronic satellite images, revealed the Iranian port in a state of change for numerous days. Dozens of freight ships as well as oil vessels waiting to unload, while lengthy lines up of vehicles created at the entry to the port going for miles, according to Naval Dome.
Rizika kept in mind that a record released by Lloyd’s of London suggested that if 15 Asian ports were hacked monetary losses would certainly be greater than $110 billion, a considerable quantity of which would certainly not be recouped via insurance coverage, as OT system hacks are not covered.
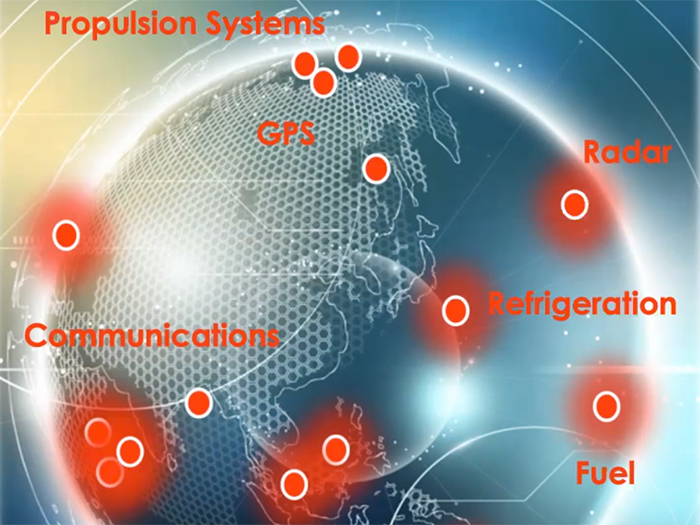
Going on clarify which components of the OT system– the network attaching RTGs, STS cranes, website traffic control as well as vessel berthing systems, freight handling as well as security as well as safety and security systems, and so on,– are under risk, Rizika claimed “all of them.”
“Unlike the IT infrastructure, there is no ‘dashboard’ for the OT network allowing operators to see the health of all connected systems,” claimedRizika “Operators rarely know if an attack has taken place, invariably writing up any anomaly as a system error, system failure, or requiring restart.”
“They don’t know how to describe something unfamiliar to them. Systems are being attacked but they are not logged as such and, subsequently, the IT network gets infected,” Rizika included. “What is interesting is that many operators believe they have this protected with traditional cyber security, but the fire walls and software protecting the IT side, do not protect individual systems on the OT network,” he claimed.
An instance would certainly be the setup of an anti-virus system on a vessel bridge navigating system (ECDIS) or, conversely, a placing system in a drifting gear DP (Dynamic Positioning), or on among the dock cranes on the pier side of the port.
“The antivirus system would very quickly turn out to be non-essential, impairing and inhibiting system performance. Antivirus systems are simply irrelevant in places where the attacker is anonymous and discreet,” claimedRizika “Operational networks, in contrast to information networks, are measured by their performance level. Their operation cannot be disconnected and stopped. An emergency state in these systems can usually only be identified following a strike and they will be irreparable and irreversible.”
Where OT networks are believed to be safeguarded, Rizika claimed they are frequently insufficient as well as based upon commercial digital system, running in an irreversible state of interference from the network or, conversely, attached to port systems as well as the devices maker’s workplaces overseas through RF radio interaction (wi-fi) or a mobile network (through SIM).
“Hackers can access the cranes, they can access the storage systems, they can penetrate the core operational systems either through cellular connections, wi-fi, and USB sticks,” claimedRizika “They can penetrate these systems directly.”
Rizika claimed that as the maritime market relocates in the direction of higher digitalization as well as enhances making use of networked, self-governing systems, relocating even more devices as well as modern technologies online, even more susceptabilities, even more technicalities, will certainly be produced.
Naval Dome likewise forecasts that cyber wrongdoers, terrorists as well as rogue states will certainly eventually start holding the atmosphere to ransom money.
“One area we see becoming a major issue is cyber-induced environmental pollution. Think about it: you have all these ships in ports, hackers can easily over-ride systems and valves to initiate leaks and dump hazardous materials, ballast water, fuel oil, etc.,” Rizika cautioned.
Offering guidance on the very first steps port drivers require to require to secure their OT systems, he claimed a deep understanding of the distinctions in between both areas is essential.
“There is a disconnect between IT and OT security,” claimedRizika “There is no real segregation between the networks. People can come in on the OT side and penetrate the IT side. We are actually seeing this now. Successful IT network hacks have their origins in initial penetration of the OT system.”
In a pre-recorded message program throughout Naval Dome’s discussion, Rear Admiral (Retd) Shiko Zana, the Chief Executive Officer of Ashdod Port, claimed: “We have become more aware of the growing cyber threat to OT systems. Naval Dome has a unique cyber defense solution capable of protecting against both internal and external cyber attack vectors. The solution provides protection for OT systems.”
Naval Dome is a cyber safety and security expert giving safety and security discovery as well as defense remedies to the worldwide maritime market. The Naval Dome service is the initial maritime multilayer cyber protection service for objective vital onboard systems as well as has actually been granted Security Level 4 Certification from category culture DNV GL.














